Developer Playground
Blog
This area is intended for a software engineer audience.

Understanding Kubernetes cgroup v2 & Deep Dive into JVM Pod Memory Issues
Explore the shift from cgroup v1 to v2 in Kubernetes and dive deep into how this architectural change triggers severe Out-Of-Memory (OOM) issues in JVM-based applications, along with practical solutions.
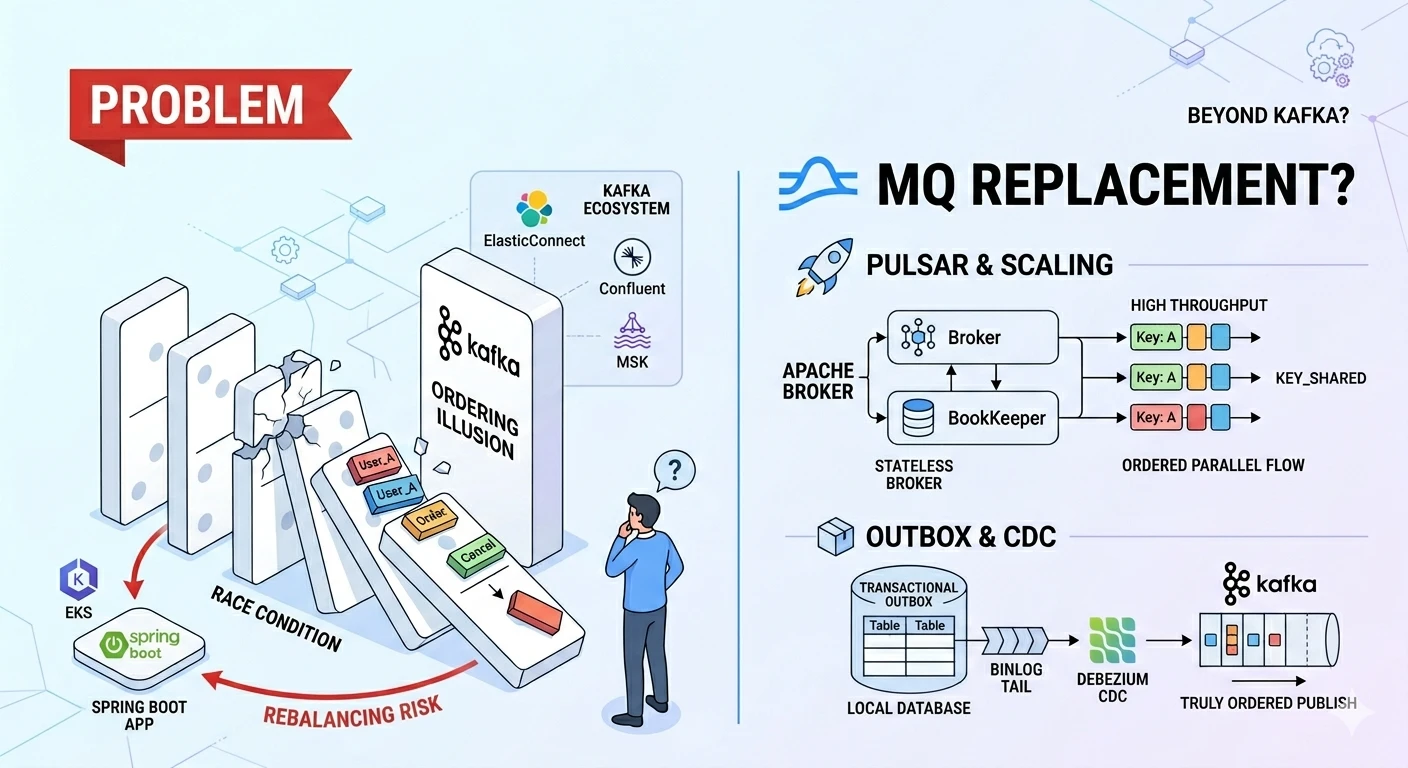
Beyond the Kafka Ordering Illusion: Is Switching MQs the Answer?
Exploring the dilemma between strict ordering and high throughput, the architectural advantages of Apache Pulsar, and why Kafka still dominates the industry landscape despite its limitations.

Spring Redis @Cacheable(sync=true): The Distributed Lock Misconception and the Salvation of JDK 25
Debunking the myth that sync=true enables distributed locks in Spring Redis, exploring its true local-lock nature in EKS architectures, and unveiling how JDK 25 resolves the infamous Virtual Thread Pinning nightmare.
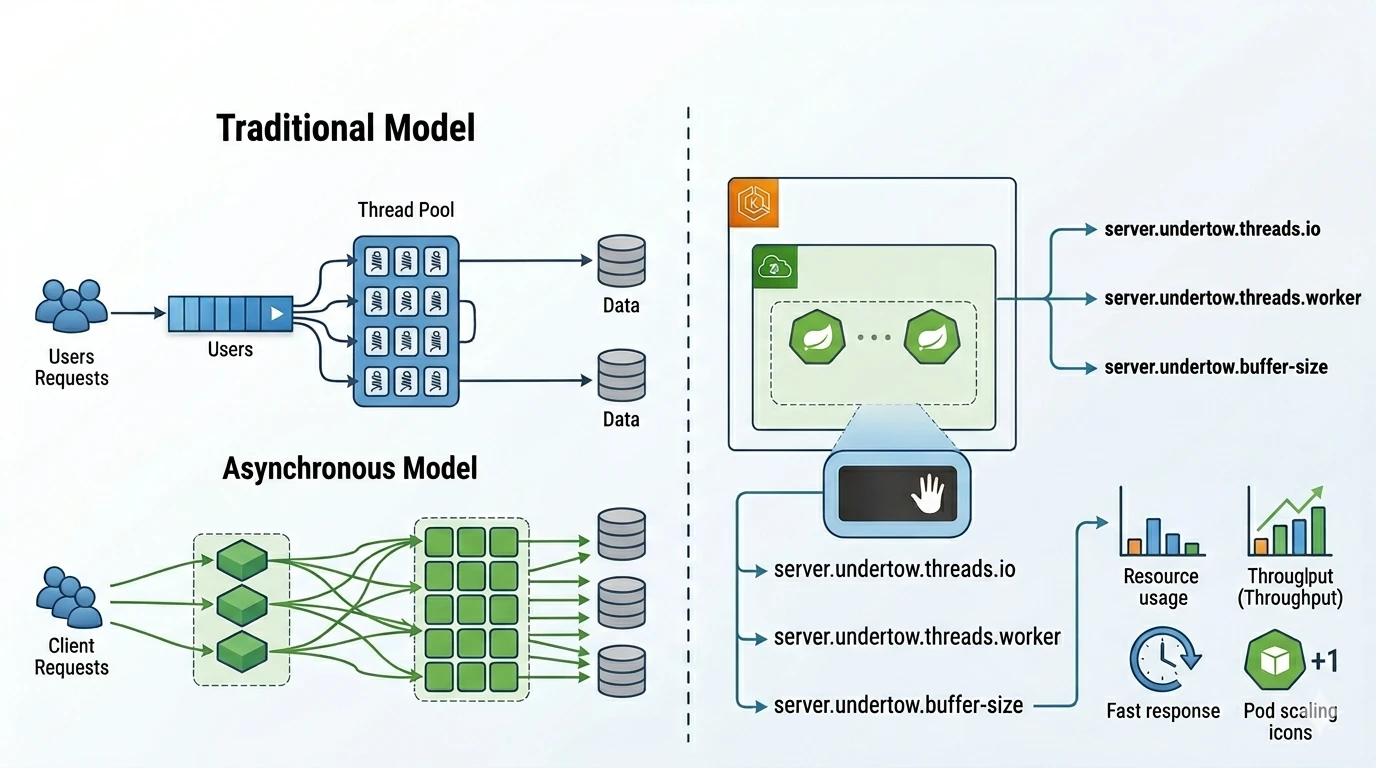
Comparing Spring Boot WAS Thread Models & Undertow Optimization in EKS
A deep dive comparing Tomcat, Jetty, and Undertow thread models, their queueing behaviors, and how to implement dynamic thread allocation and fail-fast strategies to prevent OOMKilled cascading failures in EKS.

Why 100% Event Ordering in Kafka is an Illusion
A deep dive into why relying solely on Kafka for perfect event ordering in microservices is an illusion, the underlying causes, and practical design patterns to ensure data consistency.
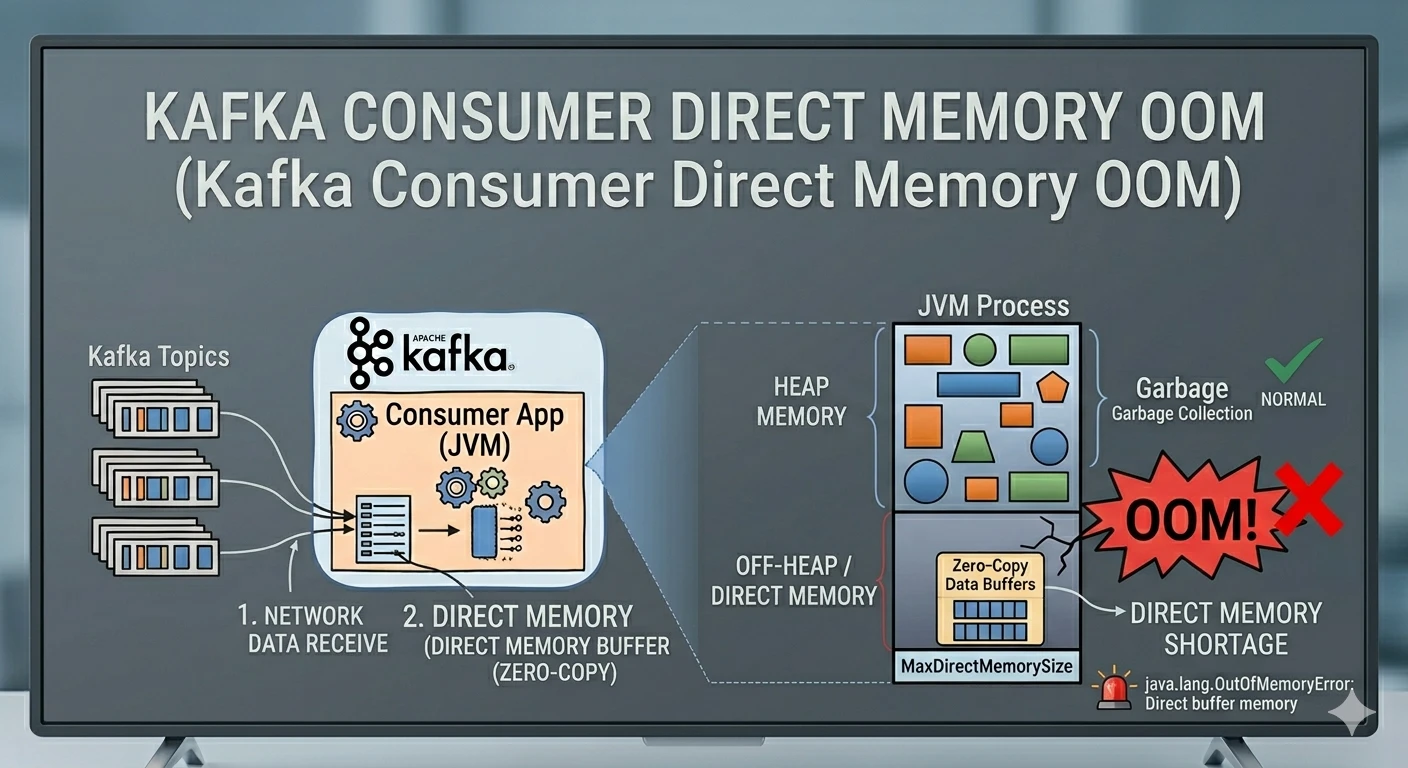
Troubleshooting Kafka Consumer: Solving Direct Memory OOM
A deep dive into diagnosing and resolving java.lang.OutOfMemoryError: Direct buffer memory issues in Kafka consumer applications by analyzing internal Kafka client code.
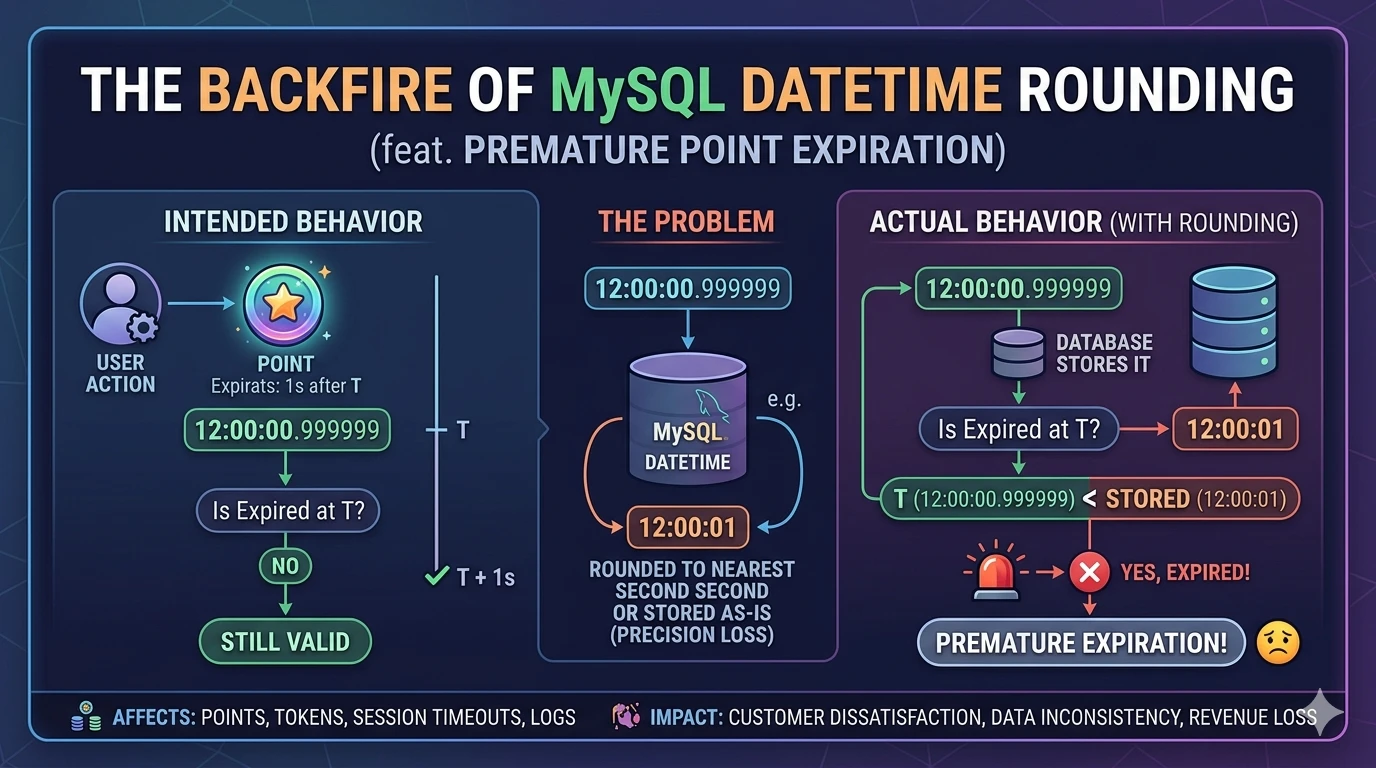
The Backfire of MySQL DATETIME Rounding (feat. A Broken 365-Day Streak)
A deep dive into data integrity issues caused by nanosecond rounding in MySQL's DATETIME and TIMESTAMP columns, and how a microsecond can break a user's daily check-in streak.
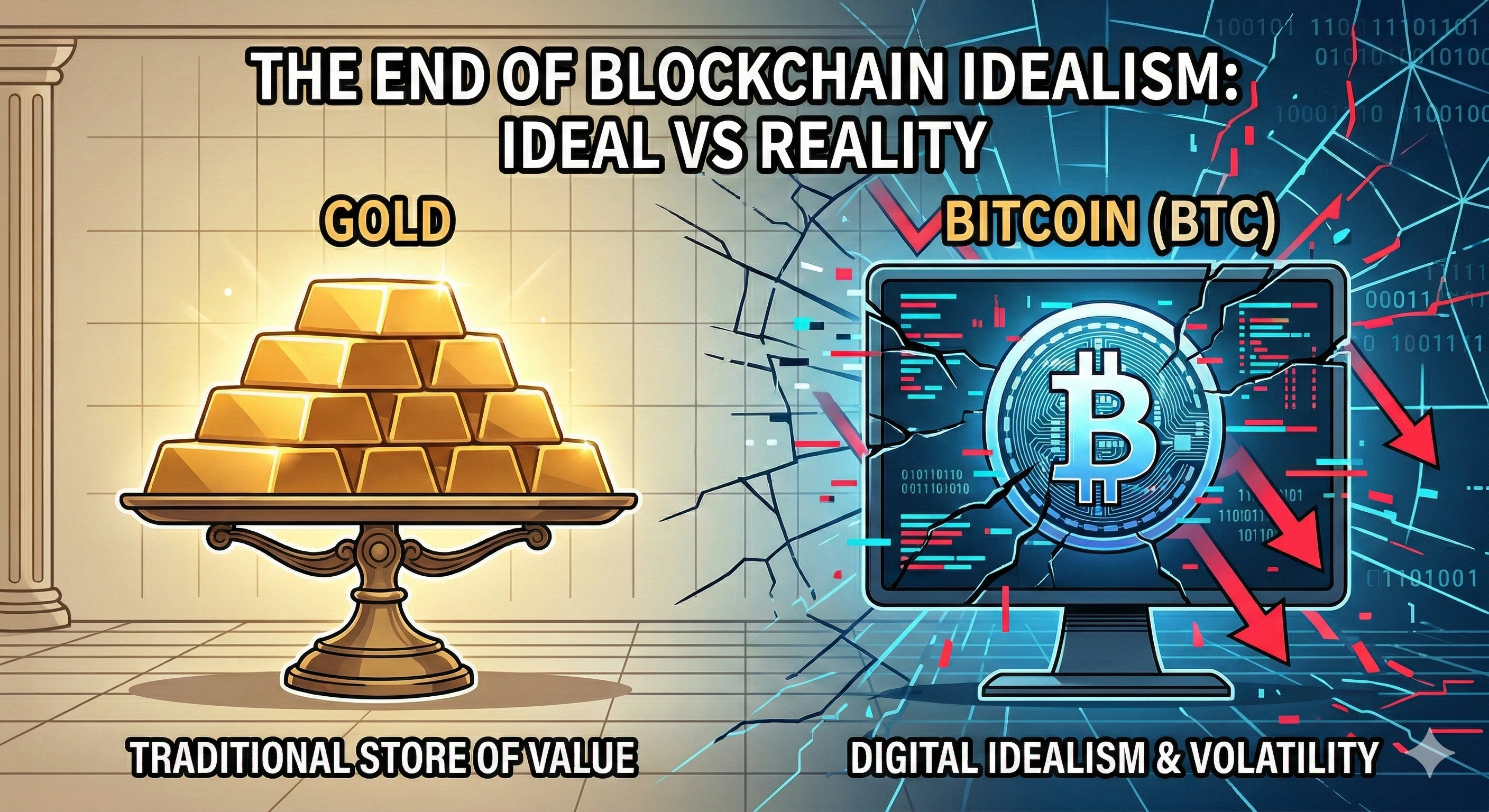
Blockchain: The End of Idealism and Survival as a Tool
A critical look at how blockchain has shifted from a revolutionary decentralized network to a pragmatic enterprise tool — examining market signals, technical compromises in L2/L3, settlement cost realities, and the rise of RWA tokenization.
Spring Actuator Port Separation: MVC and WebFlux Have Different Levels of "Isolation"
Analyzing the difference in isolation levels between MVC (Tomcat) and WebFlux (Netty) when separating Actuator ports in Spring Cloud Gateway, and presenting the correct approach for WebFlux environments.
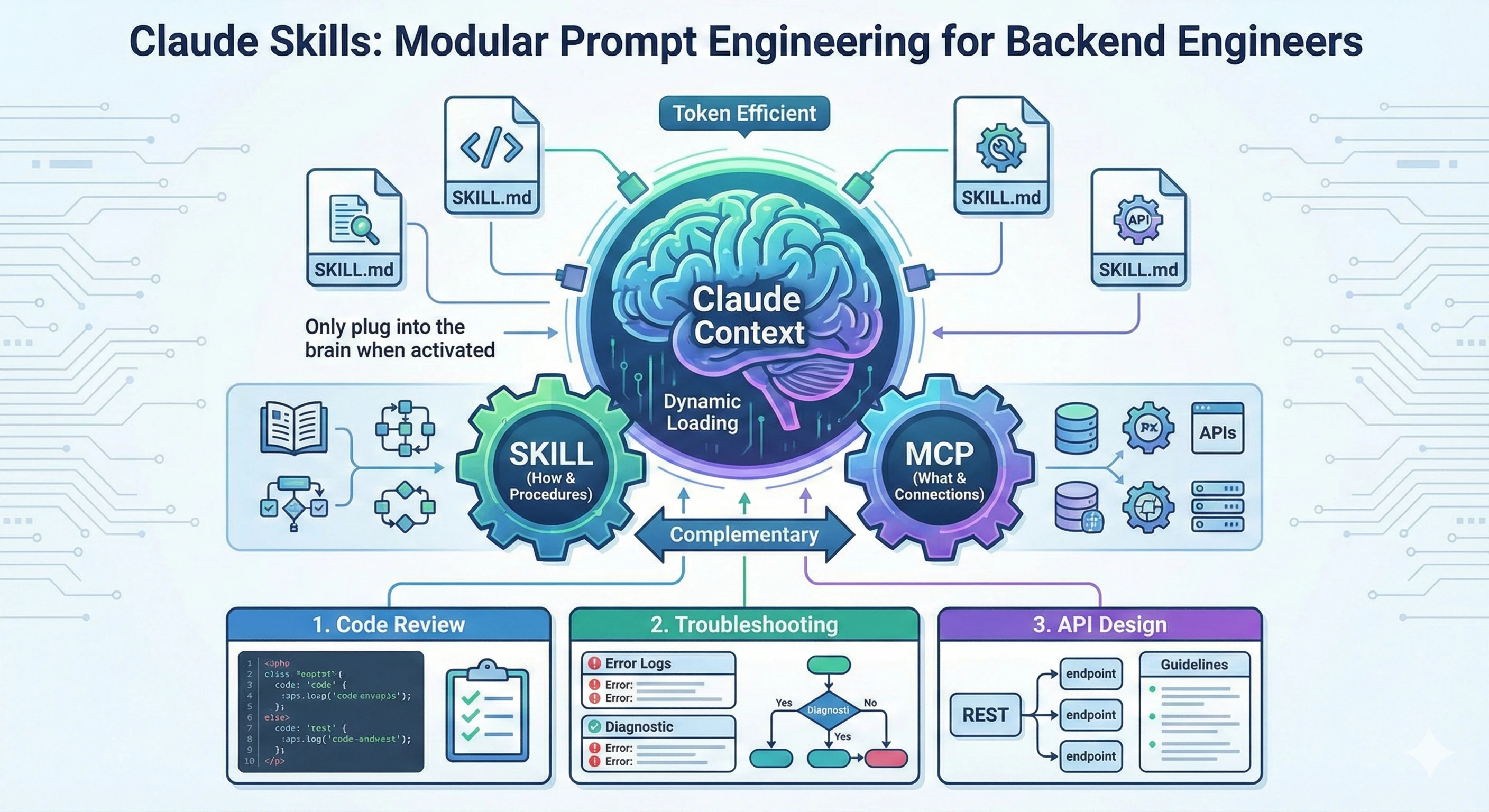
Claude Skills: Modular Prompt Engineering for Backend Engineers
Learn how Claude Skills work as reusable prompt modules, how they differ from MCP, and practical use cases for backend development workflows.
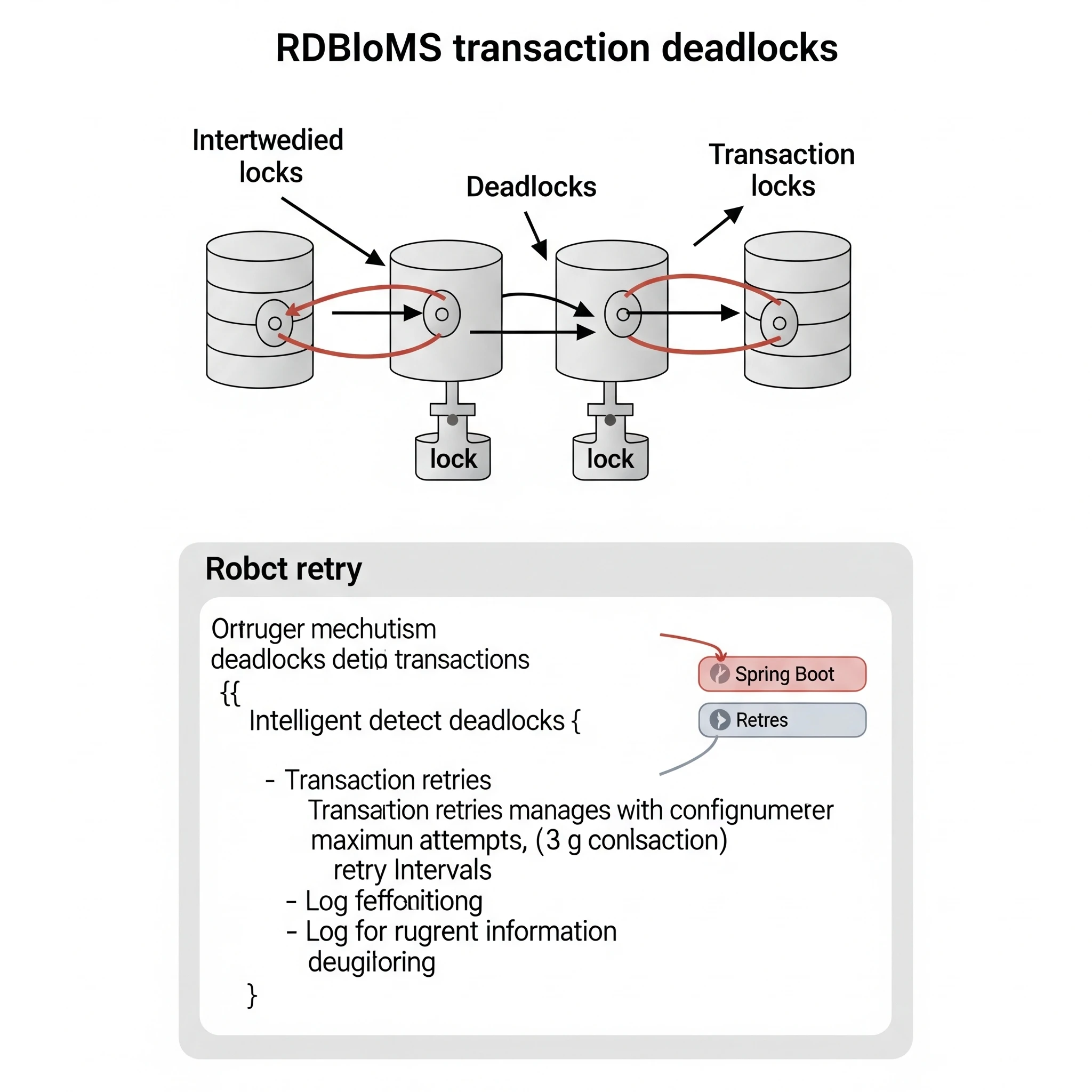
Effectively Handling RDBMS Transaction Deadlocks in Spring Boot
Learn strategies and implementation methods to prevent, detect, and recover from RDBMS transaction deadlocks in Spring Boot applications.
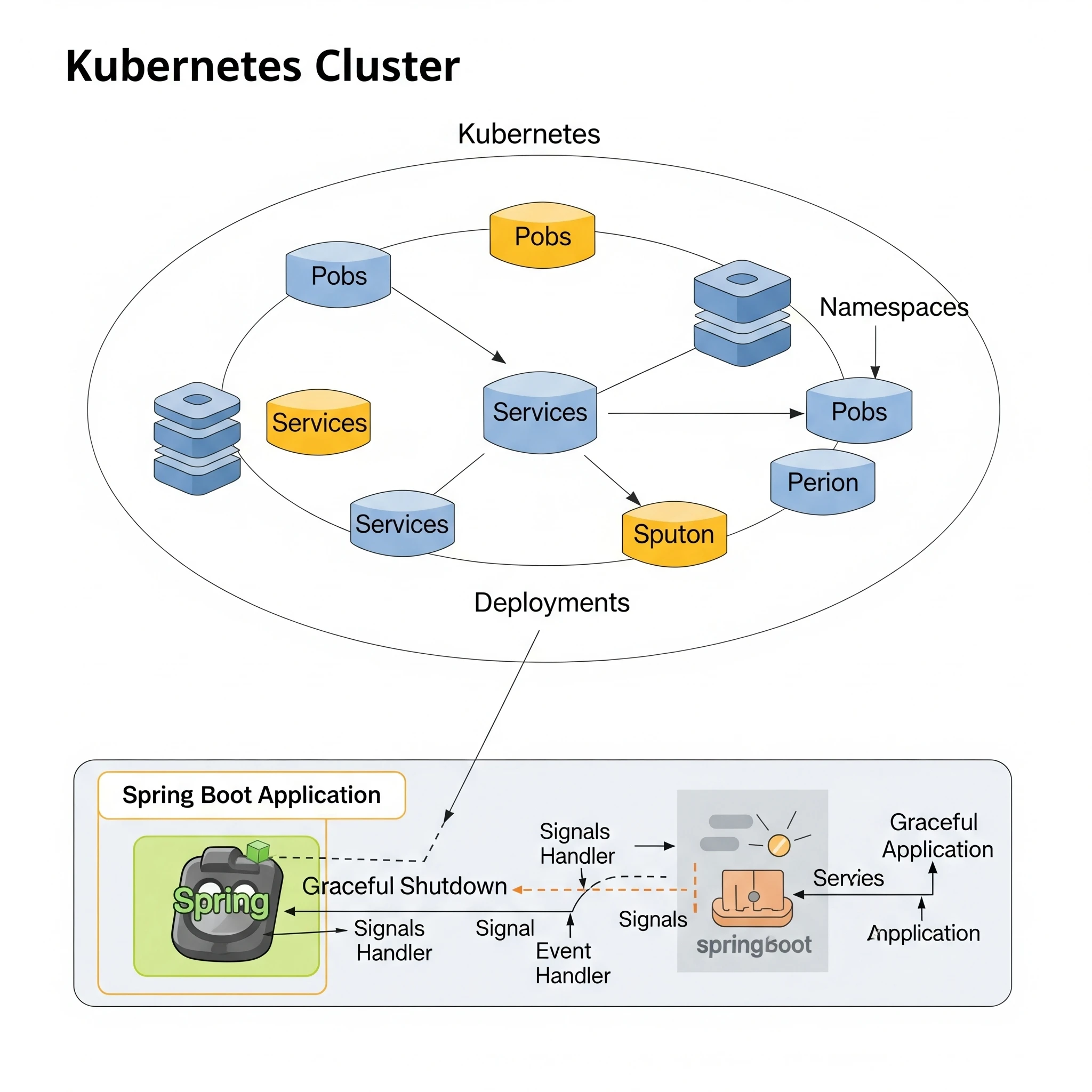
Graceful Shutdown of Spring Boot Applications in Kubernetes: SIGTERM, preStopHook, and Actuator
Learn how to gracefully shut down Spring Boot applications in a Kubernetes environment using SIGTERM, preStopHook, terminationGracePeriodSeconds, and Spring Boot Actuator.
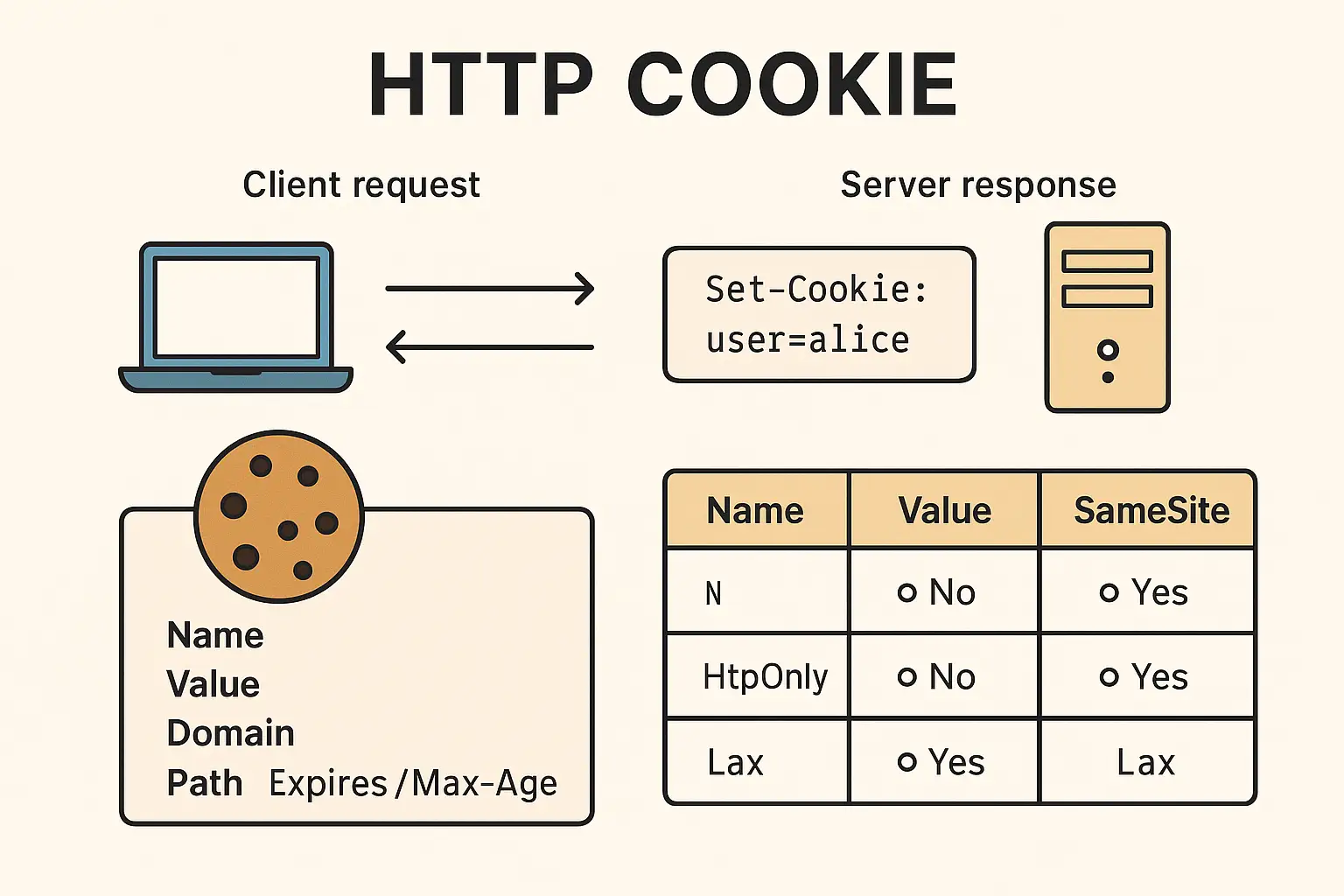
HTTP Cookie: The Core Mechanism of Web State Management
Explore the fundamentals of HTTP Cookies, their security attributes, and how they are used in modern web development.

Spring Boot on EKS: Optimizing Health Probes for Efficient Deployments
When deploying Spring Boot applications on Amazon Elastic Kubernetes Service (EKS), managing application health is crucial for reliable service operations. Kubernetes provides three types of health probes—startup, liveness, and readiness—that work together to ensure your applications start correctly, remain responsive, and handle traffic appropriately.

Distributed Locks in Spring Boot: Implementation Options and Best Practices
Distributed locks are synchronization mechanisms used in distributed systems to prevent multiple processes, services, or servers from concurrently executing critical sections of code or accessing shared resources simultaneously.
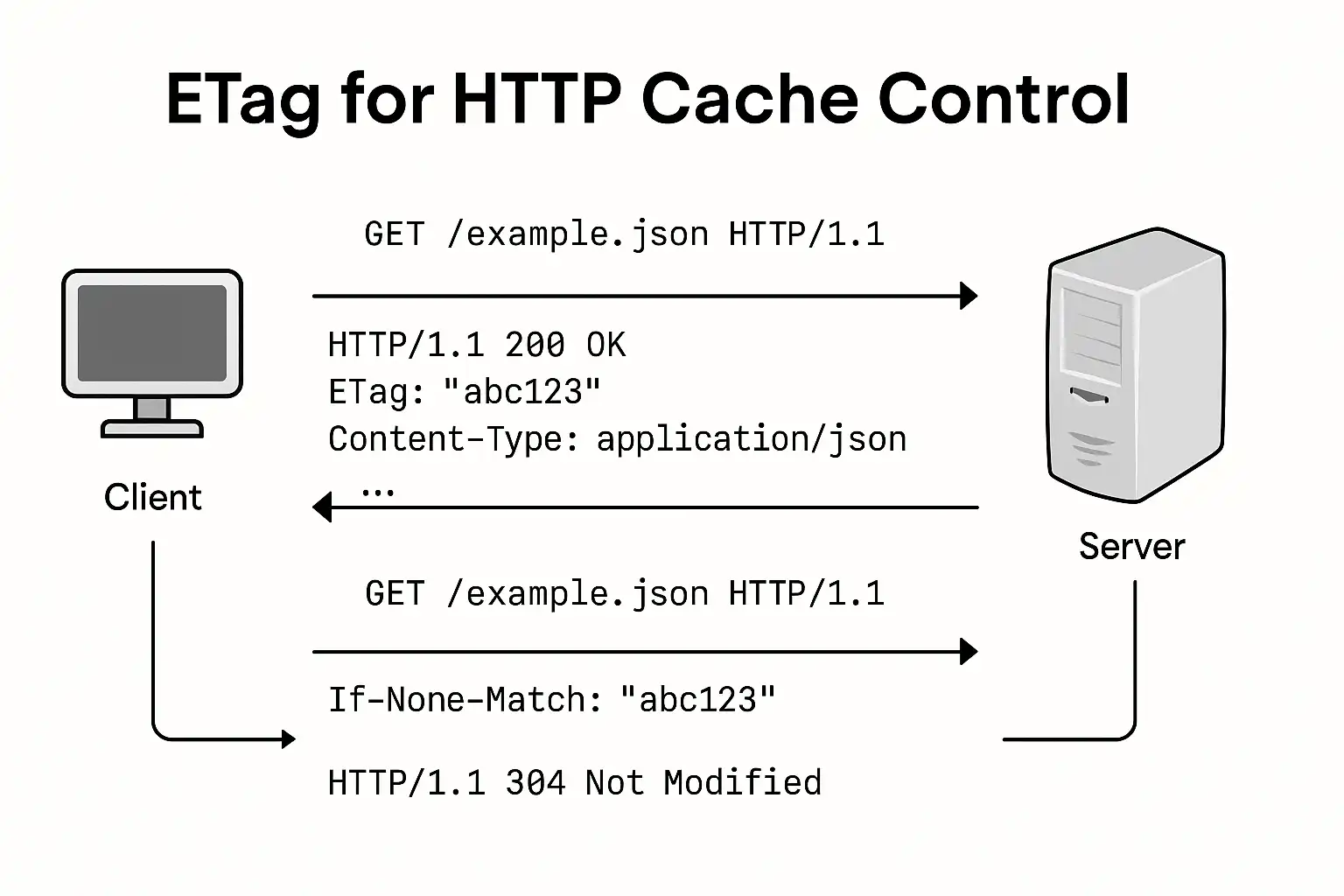
Cache Control & ETags
Cache Control & ETags: Optimizing Web Performance.
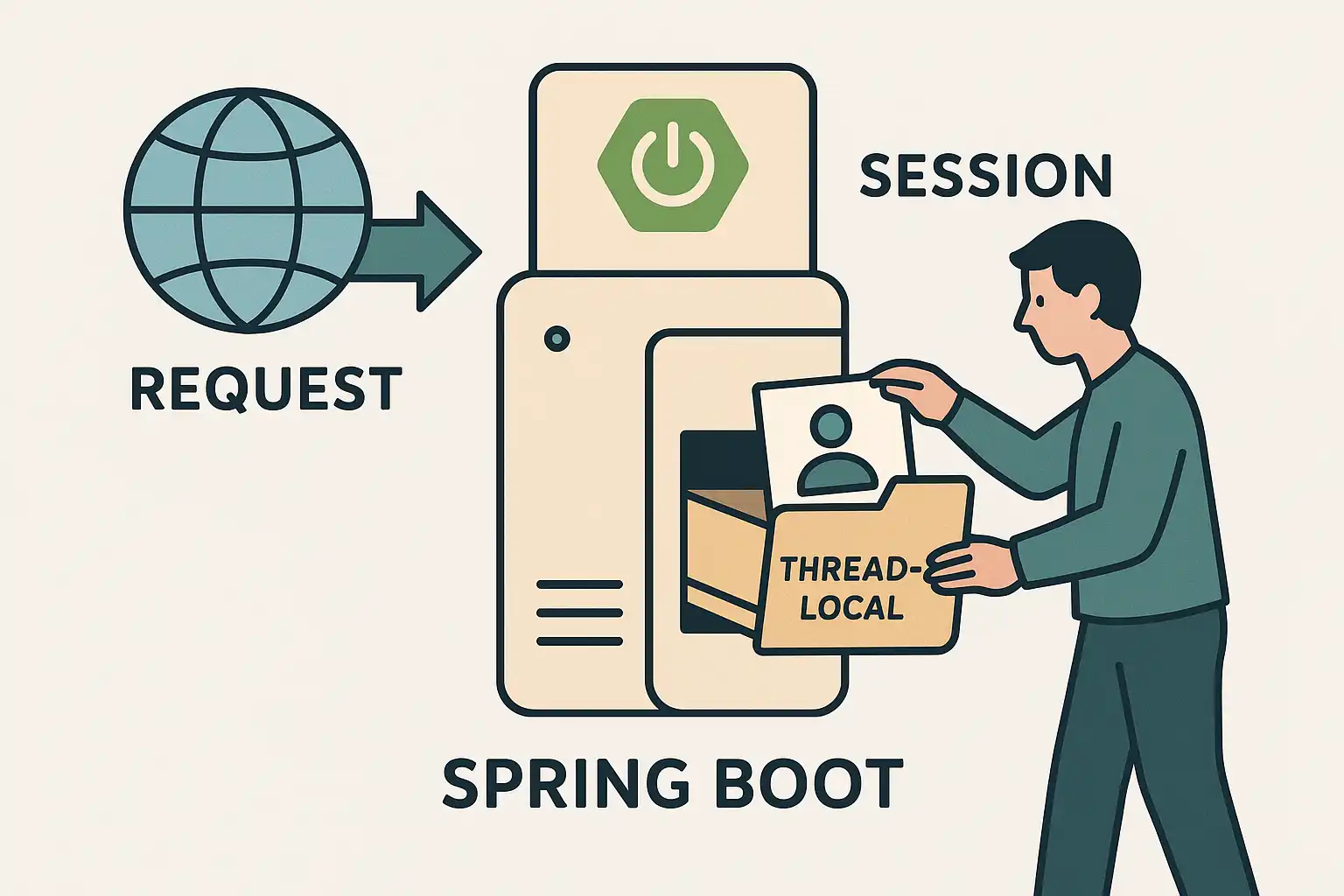
RequestContextHolder in Spring Boot: Access and Applications
RequestContextHolder is a powerful utility class in Spring Framework that provides access to the current HTTP request and response objects through a thread-local storage mechanism.

CORS (Cross-Origin Resource Sharing) & SOP (Same-Origin Policy)
Explore the concepts of CORS and SOP in web development, including how they work together to prevent CSRF attacks and how to implement CORS.

Understanding R2DBC Connection Pool
R2DBC connection pooling implements a fundamentally different approach compared to traditional JDBC connection pools like HikariCP, especially in how it handles idle connections and pool initialization.

AWS DocumentDB Comparison Analysis
Current Issues with AWS DocumentDB (Instance-Based Cluster) - Does not support zero-downtime deployments during bug fixes, increasing code-level management points
Solving Floating-Point Precision Issues
When developing financial applications or systems requiring precise calculations, floating-point precision issues can lead to critical bugs. These problems occur in JVM-based languages like Kotlin, and deciding how to store and process values, especially when interacting with databases, is a crucial design decision.

Optimizing Kafka Consumer Performance
Explore effective strategies to optimize Kafka consumer performance including partition-pod 1:1 mapping, concurrent listeners, Confluent Parallel Consumer, and asynchronous processing patterns. Learn implementation techniques, advantages, and trade-offs for each approach to maximize throughput and resource efficiency in your Kafka-based systems.
MCP Filesystem Configuration and Usage
Explore how to configure the Model Connector Provider (MCP) filesystem interface and examine real-world use cases in development environments.

How to Prevent Replay Attacks
A replay attack is a type of network attack where an attacker intercepts valid network data packets and later reuses them. By retransmitting the data, the system processes it as legitimate data. Replay attacks are difficult to detect because they appear as normal requests. Additionally, they can be successful even if the original transmission was encrypted. Replay attacks can overload systems through repetitive requests, potentially disrupting normal system operations.

About G1 GC
G1 GC has been available since Java 7 and was designated as the default garbage collector in Java 9. It is suitable for multi-processor machines with large memory.

About ZGC
ZGC performs high-cost operations concurrently without stopping application threads for more than 10ms. The pause time is independent of heap size, working effectively with heaps ranging from a few hundred megabytes to 16 terabytes.
JVM Warming Up
JVM Warming Up is a process that preloads classes into the JVM cache to improve the performance of the first request in a Java web application.

Kafka Basics
Topic, Partition, Offsets, Producer, Consumer, Delivery semantics, Broker, Zookeeper, KRaft concepts.

MongoDB Sharding Cluster with Docker Compose
Learn how to set up a MongoDB sharding cluster using Docker Compose. This guide covers the components of a sharded cluster, configuration, and step-by-step setup instructions.

Effective Identifier Generation Strategies in Distributed Environments
Generating unique identifiers in distributed systems presents significant challenges. While single-server environments can easily rely on auto-increment values or sequences, distributed environments where multiple servers must simultaneously generate IDs require careful consideration to ensure efficiency and avoid duplication.